
27/05/2021: add the http_altconnect module to prosody config to avoid errors whining about /.well-known/host-meta not being present
22/05/2021: don't enable OMEMO by default, we let the users make its own choices and it can be better
for multi-device history. I improved the apt command too (with -y --no-install-recommends).
Hi everyone,
Today we're going to install a XMPP server with a web client that is capable to
send invites links to ease the onboarding of your friends and family.
I won't explain what is XMPP in great details, because it's outside the scope of this
guide and some people will explain faaar better than me. I'm thinking about these
articles on goffi.org (french blog). For english readers, the official wiki is a good start.
tl;dr: it's a protocol made of various standards and it's possible to build
secure decentralized instant messaging networks with it. There are possibilities
to create public and private rooms too, like any popular modern instant messaging software.
Enough talking, this is what we're going to install:
Agree on a domain name: you'll replace mentions of example.com in this
guide by your chosen domain name. You'll also need subdomains: one for the web client, chat.example.com
, one for groups chats, salons.example.com, and finally another for uploading files f.example.com.
Don't forget to add type A records for these subdomains too.
First, stay on the DNS zone configuration of your registrar, we'll add some SRV and TXT type entries to ease XMPP clients and servers communications with us (more details about this on the XMPP wiki or prosody docs):
_xmpp-client._tcp.example.com 86400 SRV 1 1 5222 example.com. _xmpps-client._tcp.example.com 86400 SRV 1 1 5223 example.com. _xmpp-server._tcp.example.com 86400 SRV 1 1 5269 example.com. _xmppconnect.example.com TXT _xmpp-client-xbosh=https://chat.example.com/http-bind _xmppconnect.example.com TXT _xmpp-client-websocket=wss://chat.example.com/xmpp-websocket
NB: the left example.com is the XMPP domain, the one
on the right is the server that'll actually answer requests and you'll need a
type A record for it, not a CNAME. These records can come in handy when you want
"clean" users adresses like you@example.com but example.com is used for something
else, for example a website or mailserver, and the XMPP server is set up on xmpp.example.com .
If that's the case, change the example.com on the right to xmpp.example.com.
IMPORTANT:Log in as root before running the commands in this tutorial. We'll then configure the iptables rules to avoid eating our fingers in rage and confusion later. I'm assuming your default iptables policy is set to DROP and you have some rules set allowing you to SSH into your server:
iptables -A INPUT -p tcp -m state --state NEW -m tcp --dport 5222 -j ACCEPT # client<=>server comms iptables -A INPUT -p tcp -m state --state NEW -m tcp --dport 5223 -j ACCEPT # same as above but for encrypted ones iptables -A INPUT -p tcp -m state --state NEW -m tcp --dport 5269 -j ACCEPT # server<=>servers comms iptables -A INPUT -p tcp -m tcp --dport 80 -j ACCEPT # for access to webclient iptables -A INPUT -p tcp -m tcp --dport 443 -j ACCEPT # HTTPS iptables -A OUTPUT -p udp -m udp --dport 53 -j ACCEPT # DNS requests iptables -A OUTPUT -p tcp -m tcp --dport 80 -j ACCEPT # useful for updating packages and letsencrypt iptables -A OUTPUT -p tcp -m tcp --dport 443 -j ACCEPT # same as above but we HTTPS iptables-save > /etc/iptables/iptables.rules # pareil pour l'ipv6 ip6tables -A INPUT -p tcp -m state --state NEW -m tcp --dport 5222 -j ACCEPT ip6tables -A INPUT -p tcp -m state --state NEW -m tcp --dport 5223 -j ACCEPT ip6tables -A INPUT -p tcp -m state --state NEW -m tcp --dport 5269 -j ACCEPT ip6tables -A INPUT -p tcp -m tcp --dport 80 -j ACCEPT ip6tables -A INPUT -p tcp -m tcp --dport 443 -j ACCEPT ip6tables -A OUTPUT -p udp -m udp --dport 53 -j ACCEPT ip6tables -A OUTPUT -p tcp -m tcp --dport 80 -j ACCEPT ip6tables -A OUTPUT -p tcp -m tcp --dport 443 -j ACCEPT ip6tables-save > /etc/iptables/ip6tables.rules systemctl enable --now iptables # enable iptables services so rules persists after reboots
Next, install prosody from sources or your package manager. Two birds one stone, we'll install other needed packages too:
sudo apt-get install -y --no-install-recommends prosody nginx-full \ certbot python3-certbot-nginx \ mercurial libjs-bootstrap4 libjs-jquery
We'll now clone the prosody-modules repo from source. Some distro package managers haven't always this one up to date (looking at you, Debian, stable branch). Execute the following:
hg clone https://hg.prosody.im/prosody-modules/ /usr/lib/prosody/modules/
And here below is an updating script that you can put on your /etc/cron.daily/ folder if it exists, or root crontab. On my server, I created the following file at /usr/local/sbin/maj_prosodymods.sh:
#!/bin/sh
MODDIR="/usr/lib/prosody/modules/"
if test -d $MODDIR; then
cd $MODDIR
hg pull --update
else
mkdir -p /usr/lib/prosody
hg clone https://hg.prosody.im/prosody-modules/ $MODDIR
fi
Don't forget to flip the executable bit with chmod +x...
Then, we'll download converse.js. On Debian Buster as of 23-05-2021 there isn't an official package for it, so we'll whip up another script that we can put in a crontab. On my server, I created the file /usr/local/sbin/update_conversejs.sh with the following:
#!/bin/sh
TEMPDIR="$(mktemp -d)"
LOG=/var/log/update_conversejs.log # update log path
WWWDIR='/var/www/chat.example.com' # where static and js files will be downloaded
WWWUSER='www-data' # this value will differ on the
# distro you're using: it'll be 'http' for
# Arch Linux nginx for example.
mkdir -p $WWWDIR/dist
cd $TEMPDIR
printf "\n\n$(date) - INFO - Starting updating conversejs..." | tee -a $LOG
CURL_ERR=$(curl -s \ # get latest release tarball
https://api.github.com/repos/conversejs/converse.js/releases/latest | \
grep -o "https://.*\.tgz" | \
grep converse\.js- | \
xargs curl -fsOJL) || \
(printf "\n$(date) - ERR - Updating conversejs failed." | tee -a $LOG && exit)
# download libsignal for OMEMO support in conversejs webclient
if test -e "$WWWDIR/dist/libsignal-protocol.min.js"; then
printf "\n$(date) - TOK - Libsignal already installed, skipping." | tee -a $LOG
else
curl -fsOJL \
https://cdn.conversejs.org/3rdparty/libsignal-protocol.min.js || \
(printf "\n$(date) - ERR - Updating libsignal-protocol-javascript failed." | \
tee -a $LOG)
cp libsignal*.js $WWWDIR/dist/
fi
tar xzf *.tgz
cp -rf package/dist $WWWDIR/
sed "s/fullscreen\.html/index\.html/g" package/manifest.json > $WWWDIR/manifest.json
chown $WWWUSER:$WWWUSER -R $WWWDIR/
chmod 755 -R $WWWDIR/
rm -rf $TEMPDIR
printf "\n$(date) - TOK - Done." | tee -a $LOG
Execute this script after fitting it to your taste, it'll make you save time for step 6 because you won't have to create the $WWWDIR
It's time to launch certbot to get our certificates. I'm assuming and I hope that you already have set up A records for the main domain example.com and subdomains too (chat.example.com, f.example.com and salons.example.com) in your registrar DNS zone:
certbot certonly --agree-tos --nginx --deploy-hook "prosodyctl --root cert import /etc/letsencrypt/live" -d chat.example.com -d example.com -d f.example.com -d salons.example.com
Once it executes successfully, the certificates should be in
/etc/letsencrypt/live.
It's time we dive into prosody config files.
Open the file /usr/lib/prosody/net/http/server.lua, we'll modify it
in order to ease connecting nginx with the http interface of prosody (BOSH). In the
file, find the following line:
headers = { date = date_header, connection = response_conn_header };
and replace it by:
headers = { date = date_header, connection = response_conn_header,
access_control_allow_origin = "example.com" };
-- if 'example.com' dont fix it, replace it by '*'. Remember that your
-- XMPP server domain name goes here.
Then, we'll configure the script that'll allow us to send files to others. Execute this:
mkdir -p /var/www/upload
chown www-data:www-data /var/www/upload # l'utilisateur de nginx peut
# différer selon la distrib, faites gaffe
mkdir -p /usr/local/lib/perl
wget -O /usr/local/lib/perl/upload.pm https://raw.githubusercontent.com/weiss/ngx_http_upload/master/upload.pm
Open the downloaded file upload.pm and search for
a line like this: my $external_secret = 'it-is-secret'.
Replace it-is-secret by a strong passphrase without backslashes
or quotes to avoid crashing the script due to syntax error later.
Save or write it down somewhere, it'll be useful very soon.
Let's now get to write the prosody configuration file /etc/prosody/prosody.cfg.lua with the following:
admins = { "you@example.com" }
-- For more information see: https://prosody.im/doc/libevent
-- use_libevent = true
plugin_paths = { "/usr/lib/prosody/modules" }
modules_enabled = {
-- Generally required
"roster"; -- Allow users to have a roster. Recommended ;)
"saslauth"; -- Authentication for clients and servers. Recommended if you want to log in.
"tls"; -- Add support for secure TLS on c2s/s2s connections
"dialback"; -- s2s dialback support
"disco"; -- Service discovery
-- Not essential, but recommended
"carbons"; -- Keep multiple clients in sync
"carbons_copies";
"carbons_copies_adhoc";
"pep"; -- Enables users to publish their avatar, mood, activity, playing music and more
"private"; -- Private XML storage (for room bookmarks, etc.)
"blocklist"; -- Allow users to block communications with other users
"vcard4"; -- User profiles (stored in PEP)
"vcard_legacy"; -- Conversion between legacy vCard and PEP Avatar, vcard
"smacks";
"bookmarks"; -- old module but compatible with most clients
--"bookmarks2";
"presence"; -- see user status (online, offline, etc)
"offline";
-- Nice to have
"version"; -- Replies to server version requests
"uptime"; -- Report how long server has been running
"time"; -- Let others know the time here on this server
"ping"; -- Replies to XMPP pings with pongs
"register"; -- Allow users to register on this server using a client and change passwords
"mam"; -- Store messages in an archive and allow users to access it
"csi";
"csi_simple"; -- Simple Mobile optimizations
"csi_battery_saver";
"vjud"; -- recherche d'utilisateurs dans les salons
-- Admin interfaces
"admin_adhoc"; -- Allows administration via an XMPP client that supports ad-hoc commands
-- HTTP modules
"bosh"; -- Enable BOSH clients, aka "Jabber over HTTP"
"websocket"; -- XMPP over WebSockets
"http_altconnect"; -- BOSH and WebSocket connection endpoints discoverable via HTTP
-- Other specific functionality
"posix"; -- POSIX functionality, sends server to background, enables syslog, etc.
"limits"; -- Enable bandwidth limiting for XMPP connections
"groups"; -- Shared roster support
"server_contact_info"; -- Publish contact information for this service
"announce"; -- Send announcement to all online users
"welcome"; -- Welcome users who register accounts
"watchregistrations"; -- Alert admins of registrations
"motd"; -- Send a message to users when they log in
--"legacyauth"; -- Legacy authentication. Only used by some old clients and bots.
--"proxy65"; -- Enables a file transfer proxy service which clients behind NAT can use
}
-- These modules are auto-loaded, but should you want
-- to disable them then uncomment them here:
modules_disabled = {
-- "offline"; -- Store offline messages
-- "c2s"; -- Handle client connections
-- "s2s"; -- Handle server-to-server connections
}
motd_text = [[Hi everyone ! Welcome to my XMPP server. Have an happy chat !]]
welcome_message = "It seems it's your first logging in, $username. Welcome and enjoy your stay at $host."
daemonize = false;
pidfile = "/run/prosody/prosody.pid";
trusted_proxies = { "127.0.0.1", "::1" }
-- Force certificate authentication for server-to-server connections
c2s_require_encryption = true -- client to server require encryption
s2s_require_encryption = true -- server to server require encryption
s2s_secure_auth = true
authentication = "internal_hashed"
-- mam settings
archive_expires_after = "never" -- permanent message history
log = {
-- Log files (change 'info' to 'debug' for debug logs):
info = "/var/log/prosody/prosody.log";
error = "/var/log/prosody/prosody.err";
-- Syslog:
{ levels = { "error" }; to = "syslog"; };
}
-- http and certificate shenanigans
certificates = "certs"
-- Include "conf.d/*.cfg.lua"
legacy_ssl_ports = { 5223 }
-- http_ports = { 5280 }
-- http_interface = { "*" }
-- https_ports = { 5281 }
-- https_interfaces { "*" }
cross_domain_bosh = { "https://chat.example.com" }
cross_domain_websocket = { "https://chat.example.com" }
consider_bosh_secure = true
consider_websocket_secure = true
allow_registration = true -- needed for mod_invites
registration_invite_only = true -- registration is only permitted through invites
vjud_mode = "opt-in" -- public search is opt-in
-- https://prosody.im/security/advisory_20210512/
gc = {
speed = 500;
}
c2s_stanza_size_limit = 256 * 1024
s2s_stanza_size_limit = 512 * 1024
limits = {
c2s = {
rate = "10kb/s";
};
s2sin = {
rate = "3kb/s";
};
}
-- https://prosody.im/security/advisory_20210512/
ssl = {
key = "certs/example.com.key";
certificate = "certs/example.com.crt";
}
VirtualHost "example.com"
invites_page = "https://chat.example.com/invite?{invite.token}"
webchat_url = "https://chat.example.com/"
http_external_url = "https://chat.example.com/"
invite_expiry = 86400 * 7
http_paths = {
invites_page = "/invite";
invites_register_web = "/register";
}
modules_enabled = {
"invites";
"invites_adhoc";
"invites_page";
"invites_register";
"invites_register_web";
"http_libjs";
}
contact_info = {
abuse = { "mailto:you@example.com", "xmpp:you@example.com" };
admin = { "mailto:you@example.com", "xmpp:you@example.com" };
security = { "mailto:you@example.com", "xmpp:you@example.com" };
support = { "mailto:you@example.com", "xmpp:you@example.com" };
};
https_certificate = "certs/example.com.crt";
ssl = {
key = "certs/example.com.key";
certificate = "certs/example.com.crt";
}
Component "f.example.com" "http_upload_external"
http_upload_external_base_url = "https://f.example.com/"
http_upload_external_secret = "its-a-secret"
http_upload_external_file_size_limit = 104857600 -- limite de à 100Mo pour les envois de pjs
ssl = {
key = "certs/f.example.com.key";
certificate = "certs/f.example.com.crt";
}
Component "salons.example.com" "muc"
name = "Salons (chatrooms) chez example.com"
modules_enabled = { "muc_mam", "vcard_muc" }
muc_room_default_language = "fr"
muc_log_expires_after = "never" -- perm hist for gcs
log_all_rooms = true
muc_log_by_default = true
muc_log_presences = false
restrict_room_creation = "admin" -- only admin can create gcs
ssl = {
key = "certs/salons.example.com.key";
certificate = "certs/salons.example.com.crt";
}
As you can guess the its-a-secret value there must be replaced
by the passphrase you wrote down earlier.
Some of you probably have noticed that the user you@example.com
was listed as an admin, so let's create him with the following command line:
prosodyctl check # checks config file prosodyctl adduser you@example.com # adapt to your username@domain
We'll now start to configure our web client, converse.js. Create /var/www/chat.example.com/index.html with the following text:
<!DOCTYPE html>
<html class="no-js" lang="en">
<head>
<title>Converse</title>
<meta charset="utf-8"/>
<meta name="viewport" content="width=device-width, initial-scale=1.0"/>
<meta name="description" content="Converse XMPP/Jabber Chat"/>
<meta name="keywords" content="xmpp chat webchat converse.js" />
<link rel="manifest" href="/manifest.json">
<link type="text/css" rel="stylesheet" media="screen" href="/dist/converse.min.css" />
<script src="/dist/libsignal-protocol.min.js"></script>
<script src="/dist/converse.min.js"></script>
</head>
<body class="converse-fullscreen">
<noscript>You need to enable JavaScript to run the Converse.js chat app.</noscript>
<div id="conversejs-bg"></div>
<script>
/*
@licstart
This is free and unencumbered software released into the public domain.
Anyone is free to copy, modify, publish, use, compile, sell, or
distribute this software, either in source code form or as a compiled
binary, for any purpose, commercial or non-commercial, and by any
means.
In jurisdictions that recognize copyright laws, the author or authors
of this software dedicate any and all copyright interest in the
software to the public domain. We make this dedication for the benefit
of the public at large and to the detriment of our heirs and
successors. We intend this dedication to be an overt act of
relinquishment in perpetuity of all present and future rights to this
software under copyright law.
THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND,
EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF
MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT.
IN NO EVENT SHALL THE AUTHORS BE LIABLE FOR ANY CLAIM, DAMAGES OR
OTHER LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE,
ARISING FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR
OTHER DEALINGS IN THE SOFTWARE.
For more information, please refer to <http://unlicense.org/>
@licend
*/
converse.initialize({
auto_away: 300, // in seconds
auto_list_rooms: true,
auto_reconnect: true,
auto_xa: 600, // extended away, in seconds
bosh_service_url: 'https://chat.example.com/http-bind/',
csi_waiting_time: 60, // smartphone battery optimizations
enable_smacks: true,
locked_domain: example.com, // xmpp server that the client will only be allowed to connect to
message_archiving: 'always',
persistent_store: 'IndexedDB', // jcbrand said it'll be fast in 8.0.0 and better than localStorage
play_sounds: true,
theme: 'concord', // dark theme
view_mode: 'fullscreen',
websocket_url: 'wss://chat.example.com/xmpp-websocket', // can be unstable, if you got problems
// don't hesitate to comment it
});
</script>
</body>
</html>
This guide is almost done ! We now need to do the nginx config files.
Let's start with /etc/nginx/sites-enabled/example.com.conf:
server {
listen 80;
server_name example.com;
location / {
return 301 https://$host$uri;
}
}
server {
listen 443 ssl;
server_nam example.com;
ssl_certificate /etc/letsencrypt/live/example.com/fullchain.pem;
ssl_certificate_key /etc/letsencrypt/live/example.com/privkey.pem;
proxy_set_header Access-Control-Allow-Origin 'chat.example.com';
# this block is for the prosody's http_altconnect module
location ~* host-(meta|meta\.json) {
proxy_pass http://example.com:5280$uri;
proxy_http_version 1.1;
}
}
Next, let's continue with /etc/nginx/sites-enabled/f.example.com.conf, it's the config file for uploading files:
perl_modules /usr/local/lib/perl; # Path to upload.pm.
perl_require upload.pm;
server {
listen 80;
server_name f.example.com;
location / {
return 301 https://$host$request_uri;
}
}
server {
# Specify directives such as "listen", "server_name", and TLS-related
# settings for the "server" that handles the uploads.
listen 443 ssl http2;
server_name f.example.com;
ssl_certificate /etc/letsencrypt/live/f.example.com/fullchain.pem;
ssl_certificate_key /etc/letsencrypt/live/f.example.com/privkey.pem;
# Uploaded files will be stored below the "root" directory. To minimize
# disk I/O, make sure the specified path is on the same file system as
# the directory used by Nginx to store temporary files holding request
# bodies ("client_body_temp_path", often some directory below /var).
root /var/www/upload;
index index.html;
# Specify this "location" block (if you don't use "/", see below):
location / {
perl upload::handle;
}
# Upload file size limit (default: 1m), also specified in your XMPP
# server's upload module configuration (see below):
client_max_body_size 100m;
}
Execute nginx -t to test the config files created so far. Once no errors are detected create /etc/nginx/sites-enabled/chat.example.com.conf:
server {
listen 80;
server_name chat.example.com;
location / {
return 301 https://$host$uri;
}
}
server {
listen 443 ssl http2;
ssl_certificate /etc/letsencrypt/live/chat.example.com/fullchain.pem;
ssl_certificate_key /etc/letsencrypt/live/chat.example.com/privkey.pem;
root /var/www/chat.example.com;
index index.html;
# XMPP BOSH
location ^~ /http-bind {
proxy_pass https://example.com:5281/http-bind;
proxy_http_version 1.1;
proxy_set_header Host example.com;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_buffering off;
tcp_nodelay on;
}
# XMPP HTTP-Upload
location ^~ /upload {
proxy_pass https://f.example.com; proxy_http_version 1.1;
proxy_set_header Host example.com;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_set_header X-Forwarded-For $remote_addr;
proxy_buffering off;
tcp_nodelay on;
}
# XMPP Websockets
location /xmpp-websocket {
proxy_pass http://example.com:5280/xmpp-websocket;
proxy_http_version 1.1;
proxy_buffering off;
proxy_set_header Connection "Upgrade";
proxy_set_header Upgrade $http_upgrade;
proxy_set_header Host $host;
proxy_set_header X-Forwarded-For $remote_addr;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_read_timeout 900s;
}
# XMPP Account invite
location ^~ /invite {
proxy_pass https://example.com:5281/invite;
proxy_http_version 1.1;
proxy_set_header Host example.com;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_set_header X-Forwarded-For $remote_addr;
proxy_buffering off;
tcp_nodelay on;
}
# XMPP account register
location ^~ /register {
proxy_pass https://example.com:5281/register;
proxy_http_version 1.1;
proxy_set_header Host example.com;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_set_header X-Forwarded-For $remote_addr;
proxy_buffering off;
tcp_nodelay on;
}
# sur mon vps debian j'ai eu besoin de ça pour
# que les pages d'invitation soit bien
# formatées
location = /share/bootstrap4/css/bootstrap.min.css {
alias /usr/lib/nodejs/bootstrap/dist/css/bootstrap.min.css;
}
location = /share/jquery/jquery.min.js {
alias /usr/lib/nodejs/jquery/dist/jquery.min.js;
}
location = /share/bootstrap4/js/bootstrap.min.js {
alias /usr/lib/nodejs/bootstrap/dist/js/bootstrap.min.js;
}
}
Execute again nginx -t to spot any troubles with your config files. Once all is OK, add the line
# XMPP server domain name here, i.e it # could be xmpp.example.com in your case 127.0.0.1 example.com
in your /etc/hosts.
Restart nginx and prosody:
systemctl start prosody nginx # or prosodyctl start && nginx -s reload
Let's see the results of our work! Open a web browser and navigate
to https://chat.example.com, YMMV.
You should see something like this:

Small trick: if you want to login as
you@example.com, you can omit the right part of your adress like
this:

It's thanks to the
locked_domain parameter.
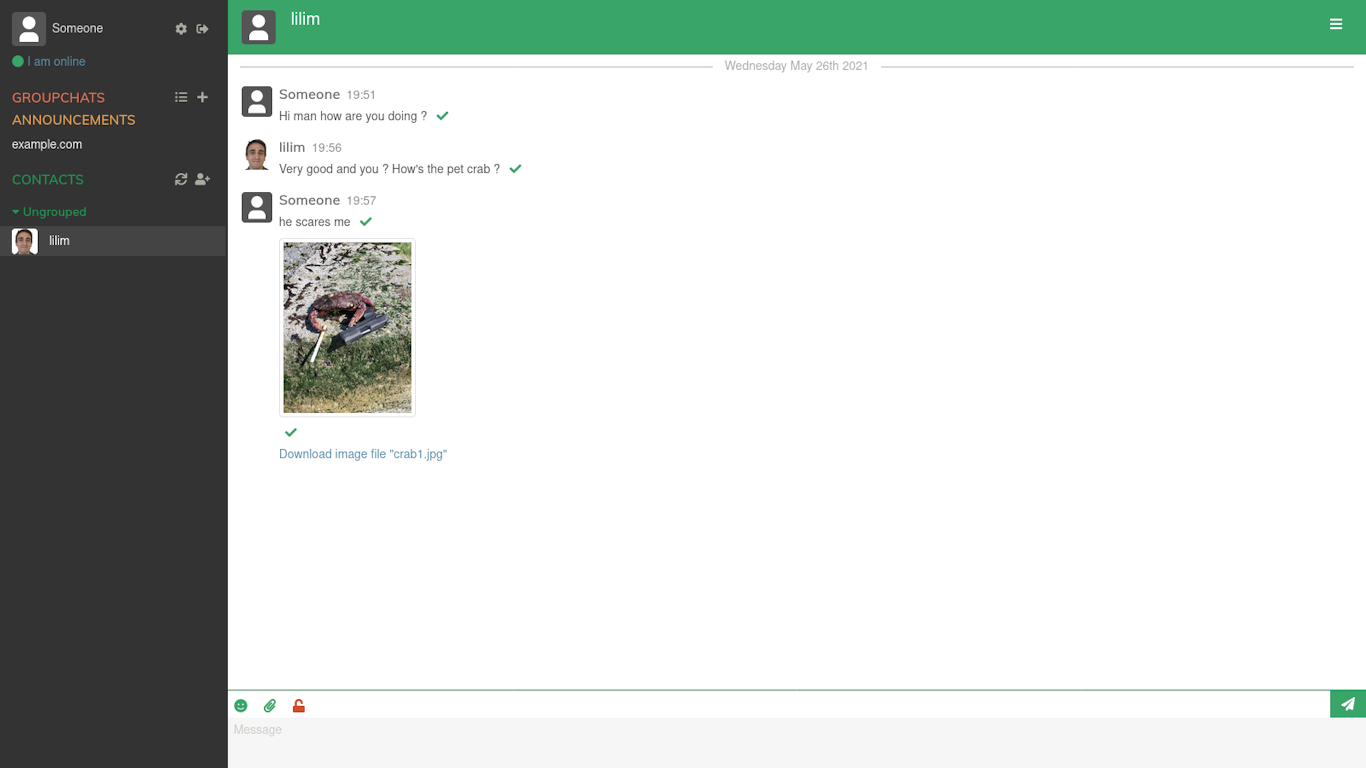
Once logged in your view should be like this:

You can then start to use XMPP and join or create group chats, add friends and chat
with them from there !
The really interesting thing is that we can create invite links from
Converse.js thanks to the admin_adhoc module.
To do so, left click on the gear icon on the top left next to your
username, then click Commands.
In the 'On which entity do you want to run commands?' field, type
in your XMPP server domain name and left click 'List available commands'.
You should have something similar to this:
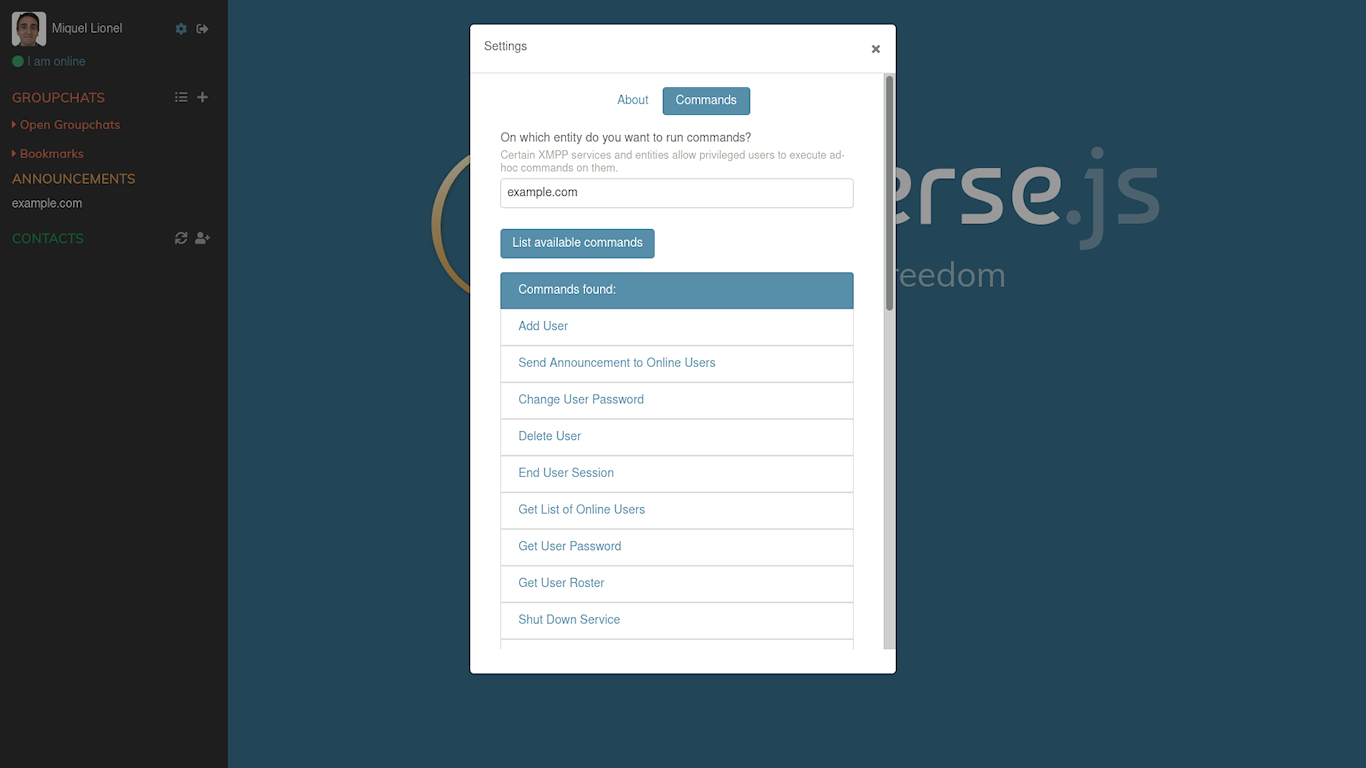
Scroll down a bit and left click on "Create new contact invite":
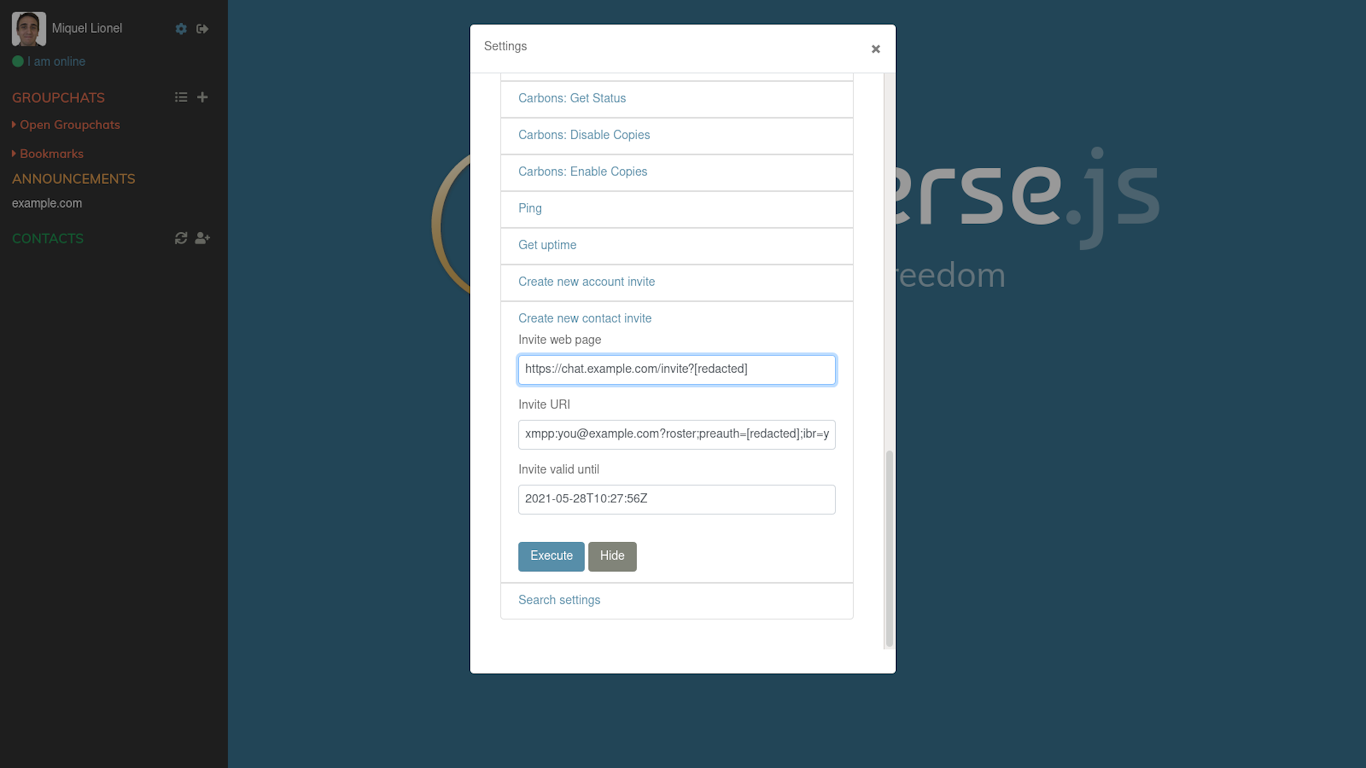
An invite link has been created ! You can now copy and send it to your
friends, family, etc...
Once opened, the link will lead to this kind of page:
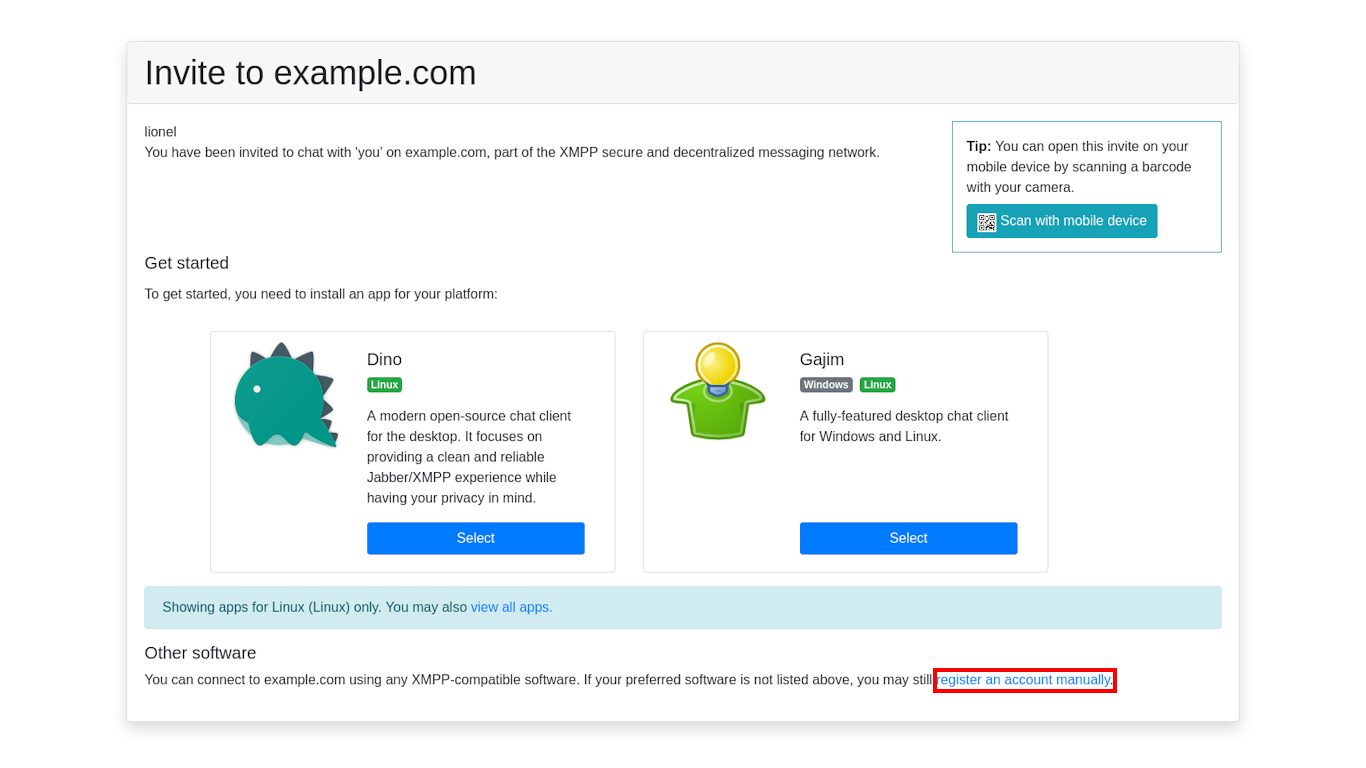
The web page auto-detects your OS platform and will
suggest you compatible XMPP software to download. In the
case you're on a smartphone, the links will download the apps
on their respective stores and continue the registration
after opening thanks to the Invite URI.
The text squared in red in the bottom left, 'register an account manually',
allows you to register via the web browser. It's handy when you want to create
an account and test it later. Here how it looks:
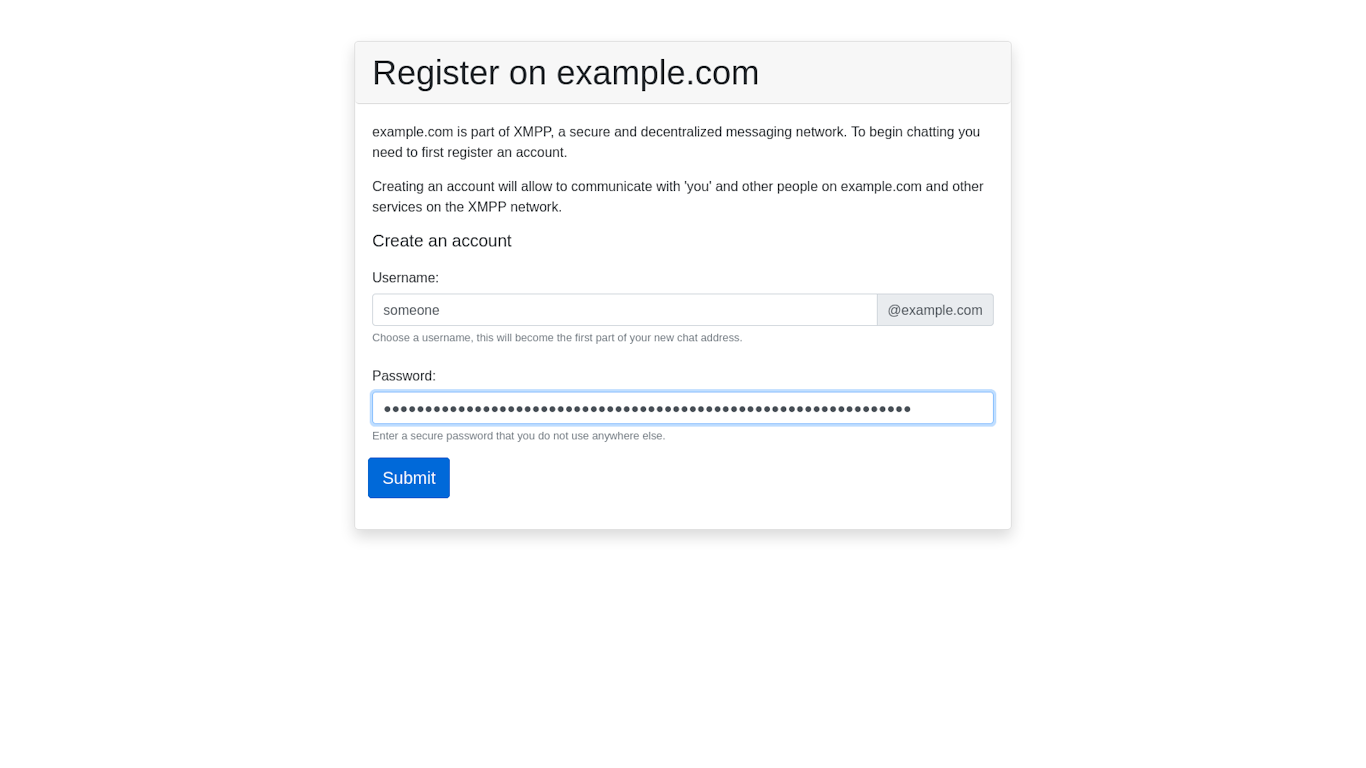
As you can see I started to fill in the form: once submitted succesfully,
you'll be greeted with this:
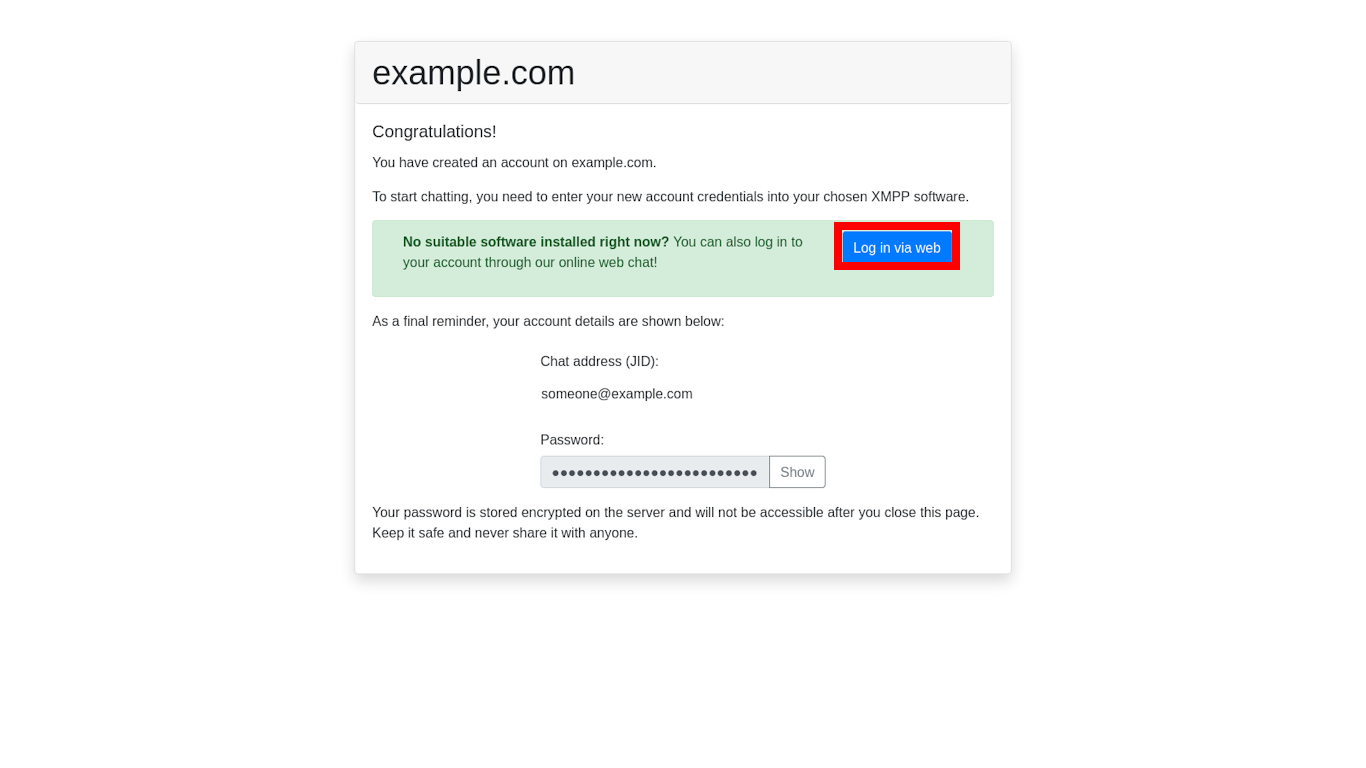
A page confirming your registration is shown, with the possibility to view your chat adress and password again to
write them down somewhere. The user can then log in with
Converse.js by clicking on the "Log in via web" button.
Once logged in, you will be added to his roster (because we did a contact invite) and he can start to chat with you.
The guide ends there! I'll get back from time to time to fix some typos and inconstencies when I spot them. I've got some notes and remarks:
Those links greatly helped me:
This wouldn't have been possible without free software and their contributors. Thanks you so much.
To be more specific:
See you soon and have a great day ! If you have any questions, remarks, suggestions or improvements to point out, don't hesitate to message me via XMPP or email at lionel ( @ ) les-miquelots ( . ) net.